配置安全策略为Portal认证的业务示例
适用的AC:AC6605、AC6005
适用的AP:所有形态的AP
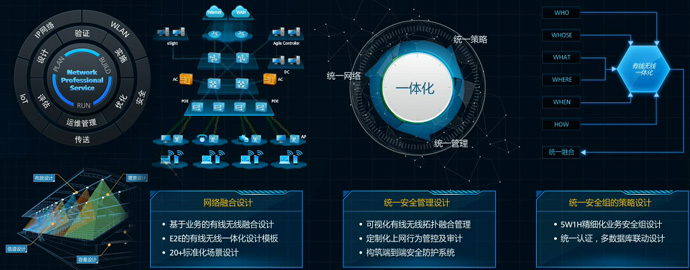
组网需求
如图1所示,现有网络中AC连接Portal服务器和RADIUS服务器,并通过接入交换机连接管理AP。
若采用802.1X认证的安全策略,管理起来比较麻烦,且由于802.1X认证中EAP协议的多样性,不适合大型网络或者多个网络的共同认证。企业希望采用Portal认证的安全策略,以达到保护网络安全统一可以统一管理网络安全的目的。
图1 配置WLAN
Portal认证组网图
| 配置项 | 数据 |
| WLAN安全 | 安全策略:SHARE-KEY认证,WEP-40加密 加密密钥:12345 |
| 服务集 | Name:huawei-1 SSID:huawei WLAN虚接口:WLAN-ESS 1 数据转发模式:隧道转发 |
| AP管理VLAN | VLAN 100 |
| AP业务VLAN | VLAN 101 |
| AC Carrier ID/AC ID | other/1 |
| AP管理IP地址池 | 192.168.10.2~192.168.10.254/24 |
| AP管理网关 | 192.168.10.1/24(AC) |
| AP用户上网公网网关 | 172.16.100.2~172.16.100.254/24 |
| AP用户上网公网地址池 | 172.16.100.1/24(AC) |
| RADIUS服务器地址 | 192.168.40.2 |
| Portal服务器地址 | 192.168.40.3 |
| DHCP服务器 | AC作为DHCP服务器,为AP和STA分配地址 |
配置流程
按照图1进行物理连接,保证AC与IP骨干网之间网络连接正常。
配置接入交换机,保证AC与AP二层互通。
在AC上配置WLAN相关业务。
业务下发至AP,用户完成业务验证。
配置注意事项
本案例只包括AC和交换机的配置,Portal服务器、RADIUS服务器的配置这里不做相关说明。
接入交换机或AC上直接接AP的端口,需要添加管理VLAN tag。AP上为零配置。
业务IP地址池给STA分配IP地址,管理IP地址池给AP分配IP地址,两种地址池需要分开配置。
需要将所有二层交换机在AP管理VLAN和业务VLAN内的下行口上配置端口隔离,如果不配置端口隔离,可能会在VLAN内存在不必要的广播报文,或者导致不同AP间的WLAN用户二层互通的问题。端口隔离功能未开启时,建议从接入交换机到AC之间的所有网络设备的接口都配置undo port trunk allow-pass vlan 1,防止引起报文冲突,占用端口资源。
操作步骤
1、配置接入交换机
# 交换机给AP管理报文加tag。配置接入交换机到AC之间VLAN 100互通。
<Quidway> system-view [Quidway] vlan batch 100 [Quidway] interface ethernet 0/0/1 [Quidway-Ethernet0/0/1] port link-type trunk [Quidway-Ethernet0/0/1] port trunk pvid vlan 100 [Quidway-Ethernet0/0/1] port trunk allow-pass vlan 100 [Quidway-Ethernet0/0/1] port-isolate enable [Quidway-Ethernet0/0/1] quit [Quidway] interface gigabitethernet0/0/1 [Quidway-Gigabitethernet0/0/1] port link-type trunk [Quidway-Gigabitethernet0/0/1] port trunk allow-pass vlan 100 [Quidway-Gigabitethernet0/0/1] quit
2、配置AC
a、配置AC,使AP与AC之间能够传输管理报文
# 配置AC,将接口GE0/0/1加入VLAN100
<AC6605> system-view [AC6605] sysname AC [AC] vlan batch 100 101 [AC] interface gigabitethernet 0/0/1 [AC-GigabitEthernet0/0/1] port link-type trunk [AC-GigabitEthernet0/0/1] port trunk allow-pass vlan 100 [AC-GigabitEthernet0/0/1] quit
b、配置AC与上层网络设备互通
# 配置AC上行接口GE0/0/2加入VLAN200。
[AC] vlan 200 [AC-vlan200] quit [AC] interface vlanif 200 [AC-Vlanif200] ip address 192.168.40.1 24 [AC-Vlanif200] quit [AC] interface gigabitethernet 0/0/2 [AC-GigabitEthernet0/0/2] port link-type access [AC-GigabitEthernet0/0/2] port default vlan 200 [AC-GigabitEthernet0/0/2] quit
c、配置AC作为AP和STA的DHCP服务器
[AC] interface Vlanif 100 [AC-Vlanif100] ip address 192.168.10.1 24 [AC-Vlanif100] dhcp select interface [AC-Vlanif100] quit [AC] interface Vlanif 101 [AC-Vlanif101] ip address 192.168.11.1 24 [AC-Vlanif101] dhcp select interface [AC-Vlanif101] quit
d、配置RADIUS服务器模板与AAA方案,并配置域信息
说明:请确保AC与RADIUS服务器的Shared-key相同。
[AC] radius-server template radius_huawei [AC-radius-radius_huawei] radius-server authentication 192.168.0.2 1812 [AC-radius-radius_huawei] radius-server shared-key cipher huawei [AC-radius-radius_huawei] quit [AC] aaa[AC-aaa] authentication-scheme radius_huawei [AC-aaa-authen-radius_huawei] authentication-mode radius [AC-aaa-authen-radius_huawei] quit [AC-aaa] domain peap.radius.com [AC-aaa-domain-peap.radius.com] authentication-scheme radius_huawei [AC-aaa-domain-peap.radius.com] radius-server radius_huawei [AC-aaa-domain-peap.radius.com] quit [AC-aaa] quit
说明:配置了domain peap.radius.com后,认证用户名后面需要加上域名。
测试用户是否能够通过RADIUS模板的认证。(已在RADIUS服务器上配置了测试用户test@peap.radius.com,用户密码123456)
[AC] test-aaa test@peap.radius.com 123456 radius-template radius_huaweiInfo: Account test succeed.
e、配置Portal Server。
[AC] web-auth-server test [AC-web-auth-server-test] server-ip 192.168.40.3 [AC-web-auth-server-test] port 50100 [AC-web-auth-server-test] shared-key cipher huawei [AC-web-auth-server-test] url http://192.168.40.3 [AC-web-auth-server-test] quit
f、在业务VLAN 101下绑定Portal服务器。
[AC] interface vlanif 101 [AC-Vlanif101] web-auth-server test direct [AC-Vlanif101] quit
g、配置AC的全局参数
# 配置AC的国家码、AC ID、运营商标识和AC的源接口
[AC] wlan ac-global country-code cn Warning: Modify the country code may delete configuration on those AP which use the global country code and reset them, are you sure to continue?[Y/N]:y [AC] wlan ac-global ac id 1 carrier id other [AC] wlan [AC-wlan-view] wlan ac source interface vlanif 100
h、配置AP并上线
# 配置AP的认证方式为MAC认证
[AC-wlan-view] ap-auth-mode mac-auth
# 根据查询到的AP设备类型ID(AP6010DN-AGN type-id为19),离线添加AP
[AC-wlan-view] ap id 1 type-id 19 mac 60de-4476-e360
[AC-wlan-ap-1] quit
# 将AP加入指定域
[AC-wlan-view] ap-region id 101 [AC-wlan-ap-region-101] quit [AC-wlan-view] ap id 1 [AC-wlan-ap-1] region-id 101 [AC-wlan-ap-1] quit
i、配置WLAN-ESS虚接口
[AC] interface wlan-ess 0 [AC-Wlan-Ess0] port hybrid pvid vlan 101 [AC-Wlan-Ess0] port hybrid untagged vlan 101 [AC-Wlan-Ess0] quit
j、配置WLAN业务参数
# 配置WMM模板和射频模板,参数采用默认配置,将WMM模板绑定到射频模板
[AC] wlan[AC-wlan-view] wmm-profile name huawei-ap1 [AC-wlan-wmm-prof-huawei-ap1] quit [AC-wlan-view] radio-profile name huawei-ap1 [AC-wlan-radio-prof-huawei-ap1] wmm-profile name huawei-ap1 [AC-wlan-radio-prof-huawei-ap1] quit
# 配置安全模板,设置安全策略为WEP认证,认证方式为共享密钥方式,加密密钥为12345
[AC-wlan-view] security-profile name huawei-ap [AC-wlan-sec-prof-huawei-ap] security-policy wep [AC-wlan-sec-prof-huawei-ap] wep authentication-method share-key [AC-wlan-sec-prof-huawei-ap] wep key wep-40 pass-phrase 0 cipher 12345 [AC-wlan-sec-prof-huawei-ap] quit
# 配置流量模板,参数采用默认配置
[AC-wlan-view] traffic-profile name huawei-ap [AC-wlan-traffic-prof-huawei-ap] quit
# 配置AP1的服务集,设置数据转发模式为隧道转发。默认转发模式为直接转发
[AC-wlan-view] service-set name huawei-1 [AC-wlan-service-set-huawei-1] ssid huawei [AC-wlan-service-set-huawei-1] wlan-ess 0 [AC-wlan-service-set-huawei-1] service-vlan 101 [AC-wlan-service-set-huawei-1] security-profile name huawei-ap [AC-wlan-service-set-huawei-1] traffic-profile name huawei-ap [AC-wlan-service-set-huawei-1] forward-mode tunnel [AC-wlan-service-set-huawei-1] quit
k、配置AP对应的VAP并下发配置
[AC-wlan-view] ap 1 radio 0 [AC-wlan-radio-1/0] radio-profile name huawei-ap1 [AC-wlan-radio-1/0] service-set name huawei-1 [AC-wlan-radio-1/0] quit [AC-wlan-view] commit ap 1 Warning: Committing configuration may cause service interruption,continue?[Y/N] y
4、验证配置结果
AP下的无线接入用户可以搜索到SSID标识为huawei的WLAN网络并正常上线。